A major step forward in protecting Quantum Key Distribution (QKD) systems from real-world threats, especially side-channel attacks, is Deep Anomaly Detection, as explained. With the use of machine learning, this innovative security system gets around the drawbacks of conventional defences and provides a reliable, flexible solution for quantum communication networks.
You can also read The Discovery of s-Ordering: Advancing Quantum Mechanics
Here’s a detailed explanation of Deep Anomaly Detection in the context of QKD security:
Core Concept and Purpose
The fundamental idea behind Deep Anomaly Detection in QKD is to train a system to recognise and describe the typical, safe functioning of a QKD network. The system is not programmed to recognise pre-established attack signatures; rather, it learns what “healthy” behaviour is. Any departure from this predetermined standard is thereafter identified as possibly malevolent. This strategy is essential because, despite their theoretical security based on quantum principles, real-world QKD systems are vulnerable to a variety of attacks that try to break the quantum protocol itself rather than by taking advantage of unexpected physical features or flaws in hardware implementations. The term “side-channel attacks” is frequently used to describe these weaknesses.
Addressing Practical Vulnerabilities in QKD
Such a system is required due to the ongoing difficulty of implementing practical QKD security. Research continuously identifies weaknesses in QKD implementations in the actual world. Physical traits such as electromagnetic emissions, detector behaviour, and timing variations can be used by attackers. Since single-photon detectors (SPDs) are essential parts of QKD systems, they are a major target of these attacks. Among the attack methods used against SPDs are:
- Manipulating detection timing
- Overwhelming detectors with light
- Exploiting detector recovery times
- Damaging detectors with lasers
In addition to SPDs, other assault vectors include inserting malicious components, manipulating wavelengths, taking use of photorefractive phenomena, and injecting light to interfere with the quantum signal. In response to the ongoing “arms race” between attackers and defenders, an anomaly detection system was developed, highlighting the necessity of constant innovation and reliable hardware in QKD.
You can also read Topological Quantum Field Theories: New TQO Class Of Models
How Deep Anomaly Detection Works
This cutting-edge security system’s Deep Support Vector Data Description (Deep SVDD) model is its fundamental component. This model is a kind of algorithm for one-class classification. The following steps make up its functioning mechanism:
Training on Normal Data: The Deep SVDD model is trained exclusively using data gathered during regular, secure QKD operations. Because it only needs instances of secure behaviour and not a wide range of attack and non-attack scenarios, this training procedure is made simpler.
Parameter Extraction: The system collects different operational parameters from the QKD configuration during a secure key exchange. The expected behaviour of the system is comprehensively profiled by these factors.
Establishing a “Safe Zone”: A “safe zone” is essentially created inside the system’s operating settings when the Deep SVDD utilises this training data to draw a border around this typical behaviour.
Real-Time Monitoring and Flagging: When the system is operating, it continuously keeps an eye on the QKD system parameters. If any parameter values deviate from the defined “safe zone,” they are promptly marked as anomalous or perhaps harmful.
Key Advantages and Benefits
A potent remedy for upcoming quantum communication networks, the Deep Anomaly Detection system has a number of noteworthy advantages over conventional countermeasures.
Detection of Previously Unknown Attacks: This is one of the method’s main advantages. Novel or “zero-day” assaults that have never been seen before can be detected since it concentrates on spotting departures from typical behaviour rather than identifying particular threat signatures. The drawback of conventional approaches, which frequently necessitate in-depth understanding of attack types, is addressed by this.
High Accuracy: Tests have revealed an exceptionally high level of accuracy, with an area under the curve (AUC) in detecting anomalies over 99%. This suggests that it is successful in differentiating between possible hazards and safe operation.
No Hardware Modifications Required: One important useful advantage of the system is that it doesn’t require any changes to the current QKD infrastructure or extra hardware. By doing this, a substantial obstacle to wider adoption is eliminated and implementation costs are greatly reduced.
Avoids Introducing New Vulnerabilities: This method doesn’t introduce new vulnerabilities into the network by blending in with existing configurations, which is a typical worry with certain conventional countermeasures.
Cost-Effective and Flexible: Its emphasis on describing typical operation makes it a strong and adaptable security solution that can defend QKD networks against a variety of present and potential threats, including ones that haven’t been detected yet.
Scalable Performance: The study emphasises that the quality and scope of the data used to characterise typical system function closely correlate with the model’s effectiveness. Accordingly, a thorough and representative training dataset is essential for achieving the best results.
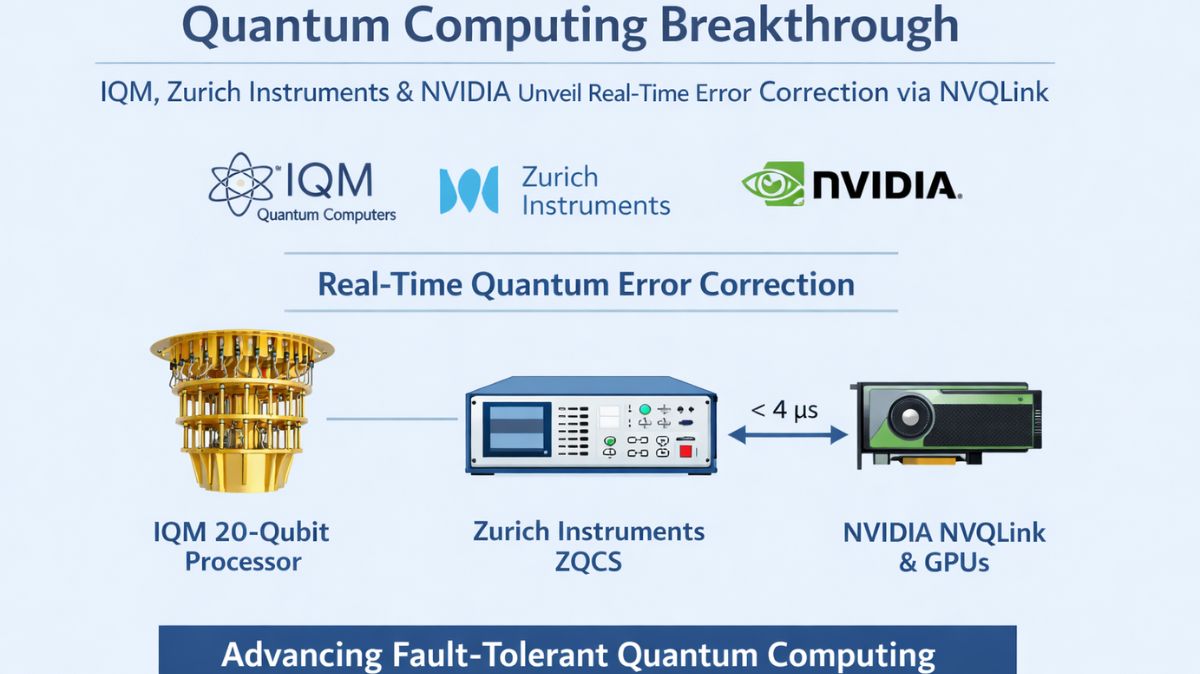
You can also read 20 Qubit Quantum Computer: The IQM Quantum Computers

Thank you for your Interest in Quantum Computer. Please Reply