A team from Johns Hopkins University has shown a major advancement in network security in a time when cyber threat detection is developing faster than traditional defenses. The “quantum revolution” offers an immediate opportunity for active defense rather than a far-off theoretical possibility. Researchers have discovered a method to surpass conventional systems in identifying the most complex cyberattacks by incorporating the current generation of “noisy” quantum processors into practical security pipelines.
The Classical Defenses: Data Drift and Feature Budgets
The cybersecurity sector has long depended on spam filters powered by conventional neural networks and Classical Neural Network Intrusion Detection Systems (NIDS). Even while these systems work well in steady settings, they are quickly reaching a “classical ceiling”. Zisheng Chen, Zirui Zhu, and Xiangyang Li’s team at Johns Hopkins found the fundamental obstacles that keep classical models from achieving complete security.
The “drift” of data is the first. Even the most resilient conventional machine learning models start to break down when network traffic patterns change and attackers use increasingly complex techniques to get over digital barriers. When the data distribution deviates from what the model was initially taught to detect, these systems frequently overlook uncommon or “borderline” threats.
Strict feature budgets present the second difficulty. It is computationally costly to analyze every single byte in real-time in the fast-paced world of global data transmission. Often, security models must compromise depth for efficiency by using condensed or limited “feature sets” in order to retain operating speed. Lastly, boundary sensitivity is a problem. Advanced contemporary attacks are made to look like real traffic, hovering just outside a model’s decision border. Classical models often fail in these “near-boundary” situations, resulting in a risky mix of false alarms and false negatives (missed attacks).
The Innovation: A Hybrid “Compress and Route” Architecture
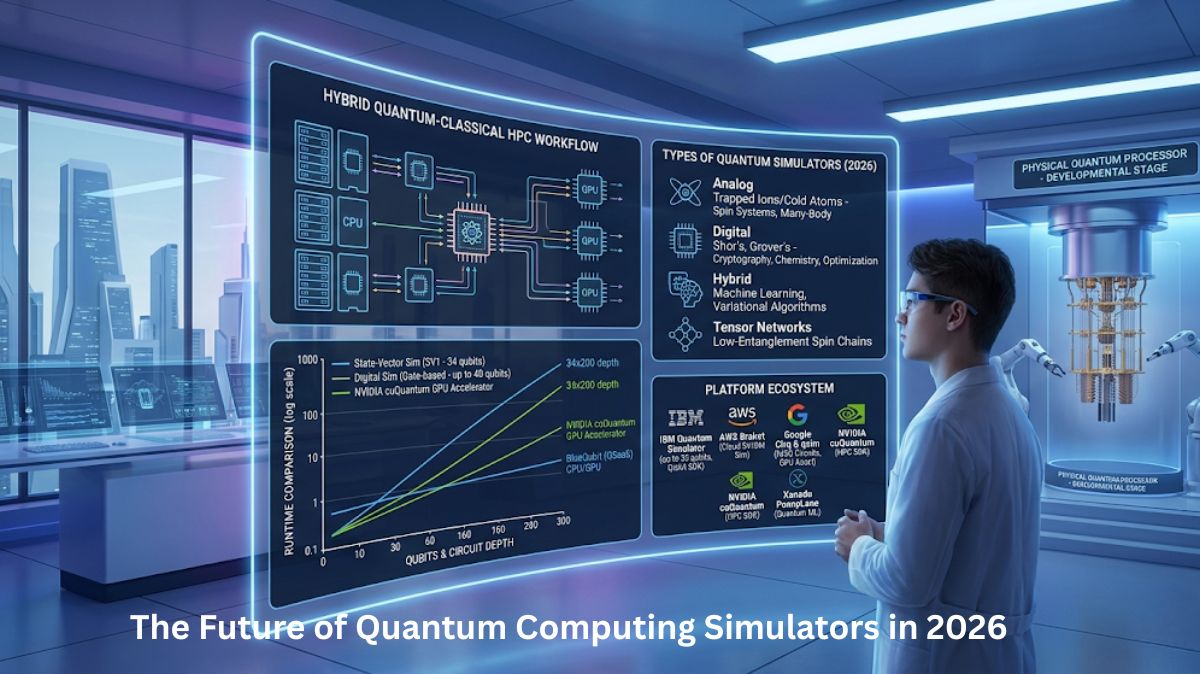
The Cyber Threat Detection Enabled by Quantum Computing,” the innovation put forth by the Johns Hopkins researchers, does not wait for the “perfect” error-corrected quantum computer of the future. Rather, it makes use of current Noisy Intermediate-Scale Quantum (NISQ) devices, despite their low qubit count and error-proneness.
The hybrid architecture at the heart of this breakthrough makes use of a “split” system to optimize the benefits of both quantum and conventional computing. An entire security model cannot presently be implemented on a quantum processor due to the extremely small number of qubits in current quantum hardware.
The researchers created a pipeline that starts with a traditional Multilayer Perceptron (MLP) in order to address this. This traditional component functions as a powerful data compressor, reducing high-dimensional, raw cybersecurity data to a small number of crucial, highly impactful aspects. The “quantum heads” are tiny quantum circuits with just two to four qubits that receive these compressed features.
These quantum heads are implemented as Variational Quantum Classifiers (VQCs) and Quantum Support Vector Machines (QSVMs). Focusing on the quantum processor’s special capacity to map data into high-dimensional “Hilbert spaces,” the system is able to produce far more complex and subtle decision boundaries than a classical model could with the same constrained quantity of data.
Proving the Concept: From Simulators to IBM Hardware
The team used two common cybersecurity datasets, NSL-KDD (for network intrusion detection) and Ling-Spam (for email spam filtering), to test their hybrid system against carefully tuned classical baselines in order to make sure the study went beyond theoretical modeling into empirical reality.
For the discipline of Quantum Machine Learning (QML), the findings were historic. The hybrid quantum-classical models regularly outperformed their all-classical counterparts in both tests. More importantly, the 4-qubit quantum models effectively decreased missed attacks and false alarms in “difficult” regimes where attacks were nuanced and near the decision limit.
By implementing their top-performing 4-qubit QSVM on a real IBM Quantum device, the researchers advanced the experiment. They used noise-aware execution strategies, such as readout error mitigation and dynamical decoupling, to take into consideration the intrinsic instability and noise of modern quantum processors.
The researchers came to the conclusion that device noise, not model design faults, was the primary cause of the remaining performance gap because the practical hardware results closely matched the simulated behavior. This demonstrated that correctly designed quantum components can serve as competitive, cost-conscious components in realistic cyber threat detection pipelines, even on tiny, noisy circuits.
The Meaning of “Quantum Advantage” in Security
The idea of the “budget” appears frequently throughout the Johns Hopkins study. A budget in the context of contemporary cyber threat detection refers to both the time and computational the needed to process threats.
The paper highlights that their quantum advantage was attained without necessitating significant improvements in preprocessing power or the size of the entire model. The researchers pointed out that even with stringent feature and qubit limits, shallow, noise-aware quantum classifiers may compete with adjusted classical baselines.
This implies that representational richness, rather than just raw speed, is the real “quantum advantage” in the NISQ era. It is the special capacity of quantum logic to identify and resolve data patterns that classical logic just cannot.
A Wake-Up Call for the Industry
The Semiconductor Engineering, this finding has significant ramifications for the development of digital defense in the future. With this work, quantum computing moves from theory to empirical, real-world application. It demonstrates that the industry can start enhancing digital defenses without waiting for thousands of error-corrected qubits.
For high-stakes computing jobs, the integration of quantum and classical systems is anticipated to become the gold standard as the 2020s go on. This emphasizes the increasing and pressing demand in the semiconductor industry for specialized hardware that can speed up data transmission between Quantum Processing Units (QPUs) and traditional CPUs/GPUs.
In the end, the results are a warning to the cybersecurity sector. This study shows that quantum computing presents an urgent defense opportunity, despite the fact that most of the discussion about it has concentrated on its potential for detecting cyber threat detection to encryption. Security experts may start creating “quantum-hardened” detection systems that keep up with a constantly changing and complicated threat landscape by adopting these hybrid designs.



Thank you for your Interest in Quantum Computer. Please Reply