Google has formally announced a ground-breaking plan to defend the HTTPS protocol on the internet from potential quantum computer threats. The goal of this project is to deploy quantum-resistant security mechanisms everywhere without sacrificing the speed or effectiveness that contemporary web users have come to expect. Google has created a technique to compress enormous volumes of cryptographic data reducing a possible 15kB of information into a small 700-byte space by using an advanced data structure called Merkle Trees.
You can also read Google Latest Quantum Computing Research 2025 breakthrough
The Looming Quantum Threat
The main driving force behind this shift is the present encryption systems’ susceptibility to quantum algorithms. Elliptic curve (EC) signatures and public keys, which are usually quite small a complete certificate chain takes up about 4 kilobytes are a major component of traditional public key infrastructure (PKI). However, Shor’s algorithm, a quantum-enabled procedure that can break public keys and forge signatures, can be used to crack these classical systems.
Attackers could use Shor’s method to fake timestamps on signed certificates, demonstrating that a certificate has been registered even when it hasn’t, if quantum computers become practical. This would make it possible to produce fake certificates, which could result in extensive web user eavesdropping. The industry has to switch to quantum-resistant algorithms like ML-DSA to combat this.
The Handshake Bottleneck
The size of quantum-resistant cryptography material, which is about 40 times larger than the classical material now in use, is a major obstacle in this shift. Web speed may suffer greatly if this enormous volume of data is transported during a TLS handshake, which is the procedure by which a browser connects to a website.
Cloudflare principal research engineer Bas Westerbaan cautioned that larger certificates result in slower handshakes. “Middle boxes” devices that reside between the browser and the destination may malfunction or perform badly as a result of this degradation. Additionally, many users may choose to disable the new encryption if it causes a considerable slowdown in browsing, leaving them unprotected. Google wants to make sure that the change doesn’t “leave people behind” by keeping the certificate size at about 4kB.
A Revolution in Data Compression: Merkle Trees
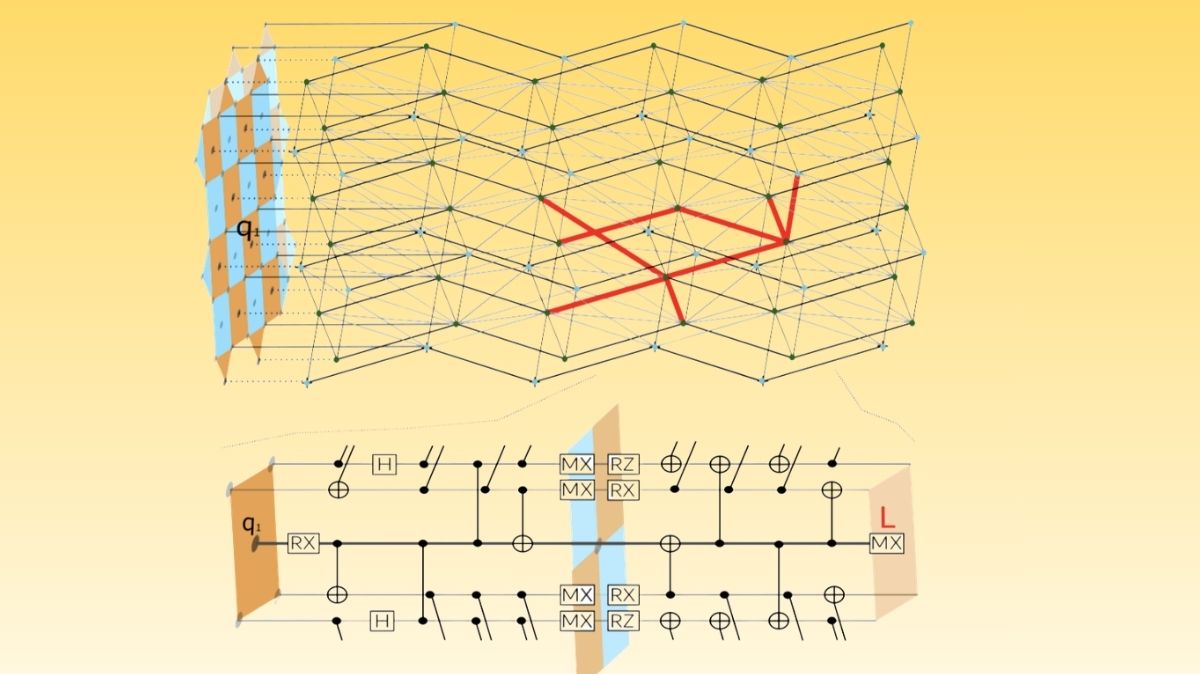
Google is using Merkle Tree Certificates (MTCs) to get around these size restrictions. Merkle Trees verify vast amounts of data with a fraction of the data needed for conventional verification procedures by utilizing mathematical concepts and cryptographic hashes.
A lengthy, serialized chain of signatures is sent to the browser in a conventional PKI. A Certification Authority (CA) issues a single “Tree Head” with MTCs, which could be equivalent to millions of separate certificates. Instead of receiving the complete chain, a browser receives a “lightweight proof of inclusion” in that tree when it connects to a website. Google is able to incorporate quantum-resistant components while maintaining data manageability and compatibility with current systems because to this technology.
You can also read IBM Heron vs Google Willow: Quantum Hardware Showdown
Lessons from History and Transparency Logs
Additionally, the transition to MTCs expands on the current Certificate Transparency logs. These logs were first put in place when DigiNotar, a CA with headquarters in the Netherlands, was hacked in 2011. 500 fake certificates were produced as a result of the hack, and some of them were utilized to snoop on Iranian internet users.
All TLS certificates are now required to be published in these open, append-only ledgers by Google and other browser manufacturers. These logs are used by website owners to make sure that their domains have not been issued any rogue certificates. To create a “quantum-resistant root store” that ensures that certificates have been published without requiring the transmission of lengthy keys and hashes, the new quantum-resistant regime will be added to the Chrome Root Store, which was established in 2022.
Implementation and Global Adoption
This approach has already started to be implemented by Google in the Chrome browser. Currently, Cloudflare is enrolling over 1,000 TLS certificates in a test distributed ledger to evaluate the effectiveness of MTCs in a real-world setting. The ledger is now generated by Cloudflare, however in the long run, Certification Authorities will assume this duty.
International standards organizations are working together on the transition. A working group named PATS (PKI, Logs, And Tree Signatures) was established by the Internet Engineering Task Force (IETF) to collaborate with important industry participants and create a long-term solution for the internet as a whole.
A Proactive Defense
The implementation of MTCs and a quantum-resistant root store is a “critical opportunity” to guarantee the stability of the contemporary web, according to a blog post from the Chrome Secure Web and Networking Team. It may take 100,000 physical qubits to crack RSA-2048 encryption but experts concur that preparation needs to begin immediately.
As Google and its partners design for the “specific demands of a modern, agile internet,” they hope to hasten the adoption of post-quantum resilience for all users. This proactive evolution guarantees that the internet’s core security will not be compromised as technology moves closer to the quantum age.
You can also read Atlantic Quantum Computing Merges with Google Quantum AI
Thank you for your Interest in Quantum Computer. Please Reply